Israel-based Hackers Show growing Sophistication of Message Attacks
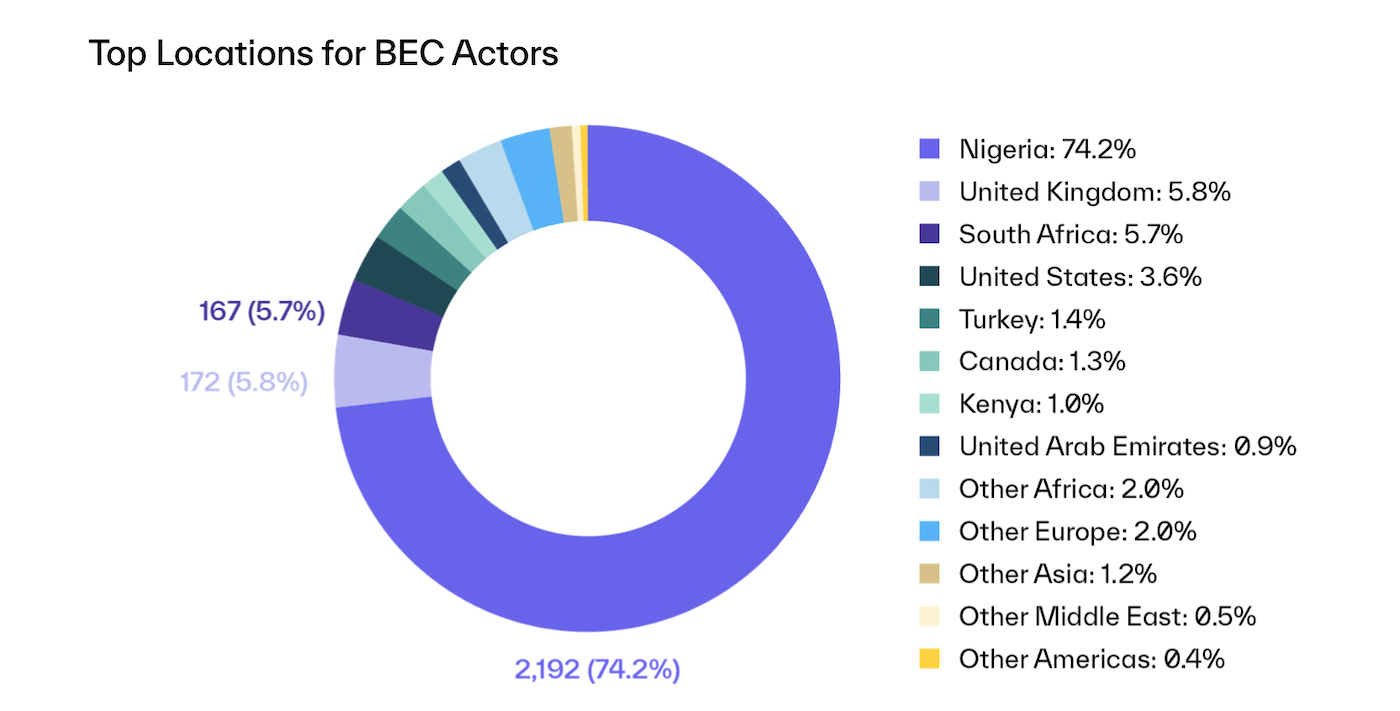
According to a report by email security firm Abnormal Security, a threat group based in Israel has recently been involved in sophisticated email attacks. This is an unusual occurrence, as the majority of attacks analyzed by Abnormal Security over the past year originated from Nigeria. The report highlights the growing sophistication of the Israeli threat actors, who have developed advanced techniques to carry out their attacks.
The attackers from Israel have been using sophisticated spoofing techniques to perpetrate business email compromise (BEC) exploits. The report tracked approximately 350 BEC exploits dating back to February 2021, all attributed to this particular group. The methods employed by the Israeli attackers include spoofing senior leaders who are responsible for financial transactions, using personas both inside and outside the target company, and even translating emails into the language commonly used by the target organization.
One notable tactic used by the attackers is to send fake emails from spoofed executives, making it appear as if the email is coming from a CEO or other high-ranking individual within the organization. This is done by updating the sending display name to mimic the CEO's name, particularly if the target organization has a DMARC policy that would typically prevent email spoofing. The attackers also make use of real domains to further deceive the recipients.
The attacks follow a specific framework involving both internal and external message vectors. The internal vectors typically impersonate high-level executives within the targeted organization, while the external vectors involve real attorneys specializing in mergers and acquisitions, often from reputable firms like KPMG. Once the initial contact is made, the attackers request an initial payment related to an impending acquisition. In some cases, the attackers even transition the conversation from email to a voice call via WhatsApp to expedite the attack and minimize the evidence trail.
The report highlights several key findings regarding these attacks. The targeted organizations are multinational enterprises with significant average annual revenue, and employees from 61 countries across six continents have received these fraudulent emails. The average amount requested in an attack is $712,000, which is significantly higher than the average BEC attack. The attackers primarily use English for their emails but also provide translations in Spanish, French, Italian, and Japanese. It is also worth noting that approximately 80% of the attacks occur in March, June-July, and October-December.
Although the attackers are based in Israel, their motivations align with those of non-state actors, primarily driven by financial gain. The report acknowledges the historical reputation of Israel as a hub for cybersecurity innovation and highlights the contrast between the country's innovation in cybersecurity and the emergence of threat actors within its borders.
The increasing severity of these BEC attacks and the higher amounts requested indicate the need for robust email security measures. Abnormal Security recommends a combination of human training to identify BEC exploits and automated defense systems that utilize behavioral AI to detect anomalies and prevent attacks before they reach their targets. With email continuing to be a lucrative attack vector, it is expected that threat actors will evolve their tactics, test new approaches, and become more targeted and sophisticated in their attempts to compromise email users. As organizations adopt communication platforms like Slack, Zoom, and Microsoft Teams, it is crucial to consider their security implications and ensure proper defenses are in place to mitigate risks.