PaperCut Ransomaware Attack
hackers have been known to exploit vulnerabilities in printer driver files, particularly those that are outdated or not updated. This type of attack allows hackers to target the infrastructure of companies or individual users and steal valuable information.
Printers are often connected to networks and computers, and their drivers act as software interfaces between the printer and the operating system. If these drivers have known vulnerabilities, hackers can exploit them to gain unauthorized access to the system.
To mitigate the risk of such attacks, it is crucial to keep printer drivers up to date by regularly checking for updates from the manufacturer. Additionally, implementing strong network security measures, such as firewalls and intrusion detection systems, can help prevent unauthorized access and protect sensitive information. Regular security audits and employee training on best practices for cybersecurity can also significantly reduce the likelihood of successful attacks.

Ransomware groups and state-sponsored cyberespionage threat actors are actively exploiting this vulnerability. The Bl00dy ransomware group has targeted educational facilities, exfiltrating data and encrypting systems. Microsoft has reported attacks by the Lace Tempest group delivering Clop ransomware using the vulnerability. Iranian state-sponsored threat actors, Mint Sandstorm and Mango Sandstorm, have also adapted the exploit in their operations.
To detect this cybersecurity threat, monitoring network traffic accessing the SetupCompleted page of a vulnerable PaperCut server is recommended. Modifying certain configuration keys or print scripts may indicate a compromise. DNS log files should be searched for domains associated with recent PaperCut exploitation. Monitoring child processes spawned from the PaperCut server and analyzing server settings and log files can help identify compromises.
To protect against this vulnerability, patching vulnerable PaperCut servers is crucial. If patching is not possible, ensure that vulnerable servers are not accessible from the internet. Block inbound traffic from external IP addresses to web management ports and apply IP address restrictions to allow only verified site servers. Keeping all systems and software up to date and patched is also important to avoid common vulnerabilities.
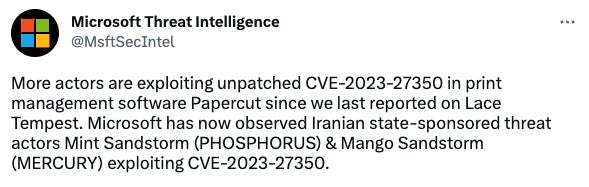
Microsoft tweets about cyberespionage threat actors
With more than 70,000 organizations using PaperCut in more than 200 countries, other threat actors became interested in exploiting this vulnerability. CISA reports that 68% of the U.S.-exposed PaperCut servers (this includes vulnerable and non-vulnerable servers) belong to the Education Facilities Subsector. PaperCut also has customers in local governments, legal, life science, healthcare and higher education, according to its website.
Microsoft tweeted on May 5, 2023, that two Iranian state-sponsored cyberespionage threat actors — Mint Sandstorm (a.k.a., Charming Kitten and Phosphorus) and Mango Sandstorm (a.k.a., Muddy Water, Static Kitten and Mercury) — have quickly adapted the exploit in their operations to achieve initial access after the public proof of concepts were published as swhown below.